
Trend Micro Cloud One – Network Security
Powerful network layer security designed for the cloud
Overview
Whether you’re starting out on your cloud migration journey or looking for defense in-depth by adding another layer of security to your environment, Trend Micro Cloud One – Network Security can provide you with network layer security in minutes.
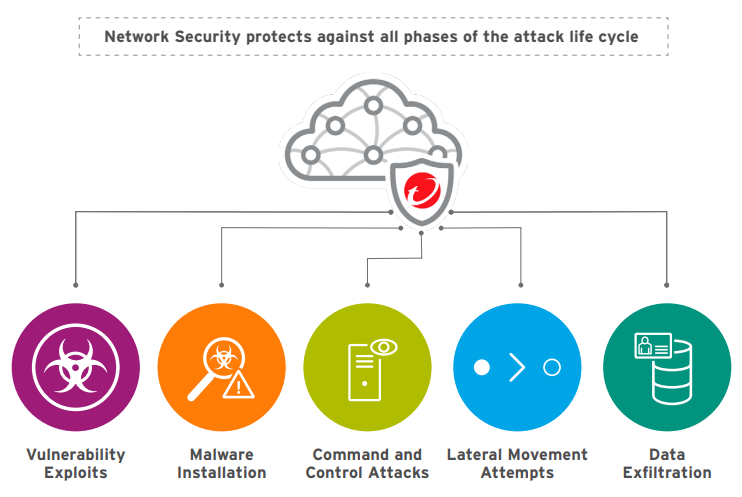
Network Security is deployed transparently within the network fabric as an actionable, inline solution. Designed to detect and prevent attacks at the network layer, for ingress, egress, and east-west scenarios, Network Security enables your organization to securely deliver business outcomes by utilizing existing architecture and processes. Gain broad runtime protection quickly against unpatched vulnerabilities and emerging threats with a single instance, so you can meet compliance requirements without the need to deploy agents or re-architect.
Using an agile deployment approach and flexible failover scenarios, your team will be empowered to protect cloud networks without disruption to your applications. Network Security gives you industry-leading coverage across multiple threat vectors, offering comprehensive protection that includes virtual patching, vulnerability shielding, exploit blocking, and high-accuracy defense against known and zero-day attacks.
Rapidly Secure Your Network in Minutes
Network Security can be transparently and easily deployed using step-by-step guidance directly in the solution. You’ll be provided with deployment templates, pre-configured filters, and security controls—giving you the tools needed to protect entire VNets and VPCs.
- Insert and remove inline without disruption
- Deploy inline within existing architecture
- Inspect ingress and egress traffic with single deployment
A Layered Security Approach
Your cloud provider has many native-security controls to help you secure your environment, including firewalls, policy and access controls, and analyzers. These tools are important, but as organizations expand their cloud operations and footprints, many are recognizing that there is a gap in network layer security.
There are several governance and compliance requirements, network security approaches, and network security controls that aren’t covered by the native solutions. Network Security can help with the following network-layer security controls and compliance requirements related to:
- Network layer virtual patching
- Egress filtering
- Deep packet inspection
- Lateral movement
Key Benefits
- Inspection at network speed: Inspect ingress and egress traffic directly inline, with network speed capabilities.
- Active and actionable security: Don’t take a passive approach to your network layer security. Protect against threats, get notified of attacks, and take action.
- Network-based virtual patching: Deploy intrusion prevention system (IPS) security at the network level to quickly provide protection from network threats, allowing you to secure your VPC and obtain compliance rapidly.
- Flexible deployment scenarios: Insert cloud network security where you need it without requiring complex cloud formation, network re-architecture, or re-IPing.
- Backed by Trend Micro Research: Get protection before vulnerability disclosure and gain advanced threat intelligence with Trend Micro Research and the Zero-Day Initiative.
Why Network Security?
Protect your cloud network and meet compliance requirements: Secure entire VPCs at scale without the need to deploy an agent with active, actionable, security that is undetectable inline. Network Security includes a flow-based engine to meet your security and networking needs while supporting governance and compliance requirements.
Cloud friendly network security: Take advantage of the best elements of the cloud though the efficient use of cloud resources and the ability to inspect traffic at the speed of your cloud network. Leverage cloud benefits such as SaaS management, consumptionbased billing, and marketplace procurement options.
Deploy simply, seamlessly, and transparently: No disruption to your business, network, applications, or DevOps processes, and stay undetectable to hackers—without losing visibility. With multiple, flexible deployment scenarios, you don’t need to rearchitect to meet your security needs. No need to deploy additional load balancers or pairs of appliances. Network Security allows you to inspect ingress and egress traffic on a single instance where you need it.
Partner confidently with your security provider: Trend Micro Research has over 500 investigators worldwide, including successful programs like the Trend Micro Zero Day Initiative, providing filters for Network Security customers, so you can protect, detect, and respond to threats faster and with greater knowledge.
Cloud security simplified: Network Security is a part of Trend Micro Cloud One, a security services platform for cloud builders. With centralized visibility and control, a unified procurement experience, and security for your cloud footprint, Network Security gives you automated, flexible, and all-in-one security.
