Overview
Organizations today are in the constant shadow of evolving and sophisticated cyber threats. In some cases, these threats are not only more complex than those of the past, but they are also targeted and rely on newly discovered vulnerabilities or exploits. In other cases, threats take advantage of older vulnerabilities that you thought were long forgotten. Safeguarding your network assets and data from such threats requires detailed visibility into all your network layers and resources. It requires comprehensive, up-to-date security intelligence, and a dynamic approach that uses awareness and automation to adapt to new threats, new vulnerabilities, and everyday network changes.
These vastly different threats require a multi-pronged approach to security. Organizations need robust security solutions at the edge of and inside their networks to prevent malicious attacks from getting to critical resources. They also need comprehensive threat intelligence to protect against known, unknown, and undisclosed vulnerabilities.
Trend Micro TippingPoint Threat Protection System (TPS) is a powerful network security platform that offers comprehensive threat protection against known and undisclosed vulnerabilities with high accuracy. TippingPoint TPS provides industry-leading coverage across different threat vectors from advanced threats, like malware and phishing, with extreme flexibility and high performance. The TippingPoint TPS uses a combination of technologies, including deep packet inspection, threat reputation, URL reputation, and advanced malware analysis on a flowby-flow basis—to detect and prevent attacks on the network. The TippingPoint TPS enables enterprises to take a proactive approach to security, providing comprehensive contextual awareness and deeper analysis of network traffic. This complete contextual awareness, combined with the threat intelligence from Trend Micro™ TippingPoint Digital Vaccine Labs (DVLabs) provides the visibility and agility necessary to keep pace with today’s dynamic, evolving enterprise and data center networks.
Pre-emptive threat prevention
TippingPoint TPS, deployed inline, has the ability to inspect and block all directions of traffic (inbound, outbound, and lateral) in real time to protect against known, unknown, and undisclosed vulnerabilities.
Threat insight and prioritization
Visibility and insight is crucial to making the best security policy decisions. TippingPoint TPS delivers complete visibility across your network and provides the insight and context needed to measure and drive threat prioritization.
Real-time enforcement and remediation
Defend the network from the edge, to the data center, and to the cloud with realtime, inline enforcement and automated remediation of vulnerable systems. TippingPoint TPS achieves a new level of inline, real-time protection, providing proactive network security for today’s and tomorrow’s real-world network traffic and data centers. The Threat Suppression Engine (TSE) architecture performs high-speed, inline deep packet traffic inspection, and the purpose-built appliance’s modular design enables the convergence of additional security services.
Operational simplicity
With flexible deployment options that are easy to set up and manage through a centralized management interface, TippingPoint TPS provides immediate and ongoing threat protection with outof-the-box recommended settings.
Features
Threat Prevention
Go beyond next-gen IPS with real-time detection, enforcement, and remediation
TippingPoint integrates with the Deep Discovery Advanced Threat Protection solution to detect and block targeted attacks and malware through preemptive threat prevention, threat insight and prioritization, and real-time enforcement and remediation.
- Inspect and block inbound, outbound, and lateral network traffic in real time
- Defend the network with real-time, inline enforcement and automated remediation of vulnerable systems
- Use machine learning techniques to make real-time decisions to immediately and accurately block malicious traffic
Dynamic Scalability
Performance scalability and flexibility for the most demanding network requirements
Delivers unprecedented security and performance for high-capacity, high-performance enterprise networks. It scales performance requirements to protect data, critical infrastructures, and vulnerable applications in real time without adversely affecting network performance and is designed to follow your network wherever it moves whether it’s physical or virtual.
- Scale performance from 250 Mbps up to 120 Gbps
- Deploy up to 40 Gbps inspection throughput in a market-leading 1U form factor
- Embraces software-defined network protection by deploying IPS as a service
Deep Inspection
Comprehensive threat insight and prioritization
Gain complete visibility across your network with the insight and context needed to measure and drive vulnerability threat prioritization. Deep inspection of network traffic identifies and blocks threats undetected by traditional security solutions.
- Eliminate SSL blind spots by inspecting encrypted traffic without compromising network performance
- Submit potential indicators of compromise (IoC) to Deep Discovery for advanced threat analysis
- Monitor and block URL suspicious objects with additional support for user-provided malicious entries
Flexible Deployment
Deployment flexibility and investment protection
With flexible deployment options that are easy to setup and manage through a centralized management interface, TippingPoint provides immediate and ongoing threat protection with out-of-the-box recommended settings.
- Simplify security operations with flexible deployment options that are easy to setup and manage
- Reassign licenses across TPS deployments without changing network infrastructure
- Easily scale performance and security requirements with pay-as-you-grow licensing model
Deployment
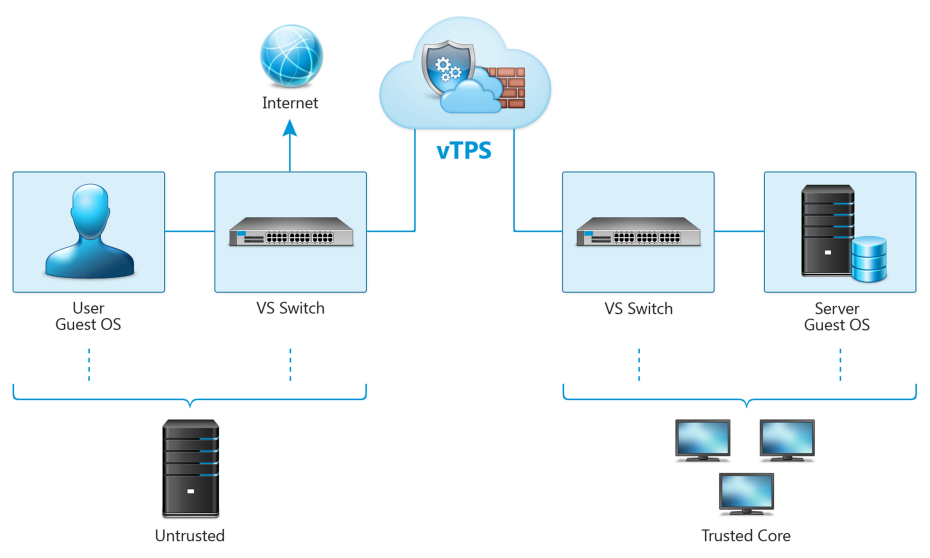
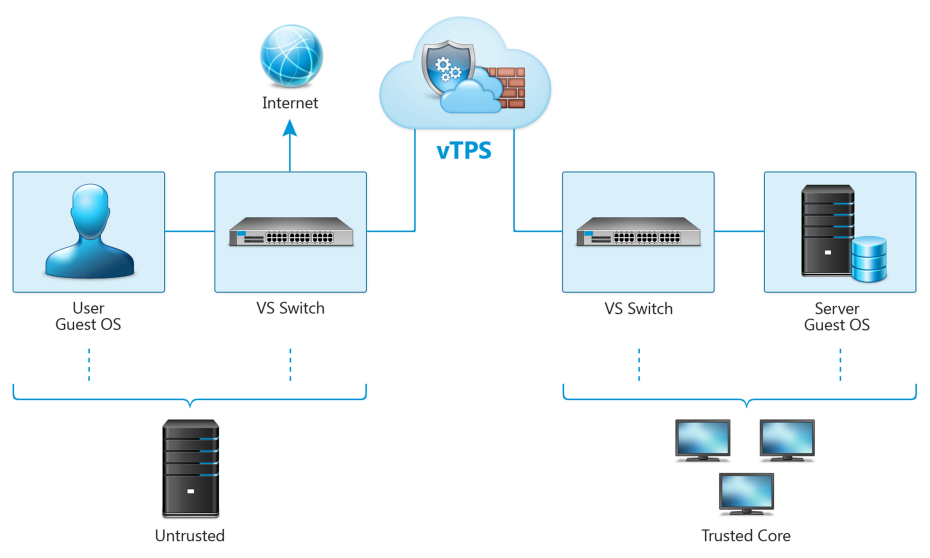
Use the configuration steps in these topics to deploy a TippingPoint Virtual Threat Protection System (vTPS) virtual appliance in either a VMware or kernel-based virtual machine (KVM) environment. The vTPS virtual appliance is a software appliance designed to give you the same level of functionality available in the TippingPoint Threat Protection System (TPS), but virtually rather than physically. Just as with a TPS device, the vTPS virtual appliance protects your network with the Threat Suppression Engine (TSE) by scanning, detecting, and responding to network traffic according to the filters, action sets, and global settings you maintain on the vTPS virtual appliance. You can share the same policies across virtual and physical deployments, and you can centralize the management of your deployments with a Security Management System (SMS) or a virtual SMS (vSMS).
After you deploy the vTPS virtual appliance, access the appliance by using the Local Security Manager (LSM) web interface or your SMS client. Learn more about these interfaces from the TPS product documentation.
Functionality
The Virtual Threat Protection System (vTPS) virtual appliance is a software-based security appliance that can inspect traffic in a virtual network between Layer 2 broadcast domains. With few exceptions, the vTPS platform is designed to be functionally identical to a physical TPS device.
The vTPS virtual appliance has most of the same features as the TPS device, including:
- In-line, real-time threat protection for inbound IPv4 traffic that is SSL encrypted (Performance mode only)
- HTTP response processing to decode URL encodings and numeric character references
- DNS reputation remediation for enabling NXDOMAIN (name does not exist) responses to clients that make DNS requests for hosts that are blocked
- Layer 2 Fallback (Intrinsic High Availability)
- Enhanced SNMP support
- The ability to collect a client's true IP address.
- The ability to identify the HTTP URI and hostname information associated with an event.
- Flexibility to upgrade inspection throughput from 500 Mbps to 2 Gbps. For successful TPS functionality in a virtual environment, the vTPS virtual appliance:
- Supports Layer 2 IPS deployments—The vTPS virtual appliance connects the virtual switches. Traffic between the virtual switches is bridged on these connections using promiscuous mode.
- Provides full protection of North-South traffic.
- Provides limited protection of East-West traffic (according to existing network policy constructs).
For optimal deployment of your vTPS virtual appliance, you should note the specific areas in which your virtual appliance functionality differs from a physical TPS device.
Specifications
Because the vTPS virtual appliance is a virtual product, the out-of-box experience (OBE) for vTPS users is described in an email from Trend Micro TippingPoint. This email contains licensing and activation information and directs you to use the license manager on the Threat Management Center (TMC) to create and download vTPS certificate packages.
When setting up your vTPS virtual appliance, note the following:
- The vTPS virtual appliance initially starts up in vTPS Trial Mode. Trial Mode is primarily exploratory and comes with a limited number of security filters in the Digital Vaccine package. In this mode, an SMS can manage only one vTPS virtual appliance at a time. Because Trial Mode has a fixed serial number and entitlement, you cannot use Trial Mode to perform TippingPoint Operating System (TOS) upgrades or distribute Digital Vaccines.
- The vTPS virtual appliance remains in Trial Mode until you install a valid certificate for vTPS Standard Mode. Learn more on upgrading to vTPS Standard Mode,
- The vTPS virtual appliance does not support a hitless reboot or hitless upgrade. Traffic flow is interrupted until the boot sequence completes because, unlike on a TPS device, the network ports on a vTPS virtual appliance are virtual.
The following table highlights the ways in which getting set up on a TPS device and vTPS virtual appliance are different:
| |
vTPS Standard |
vTPS Performance |
| Supported IPS Inspection Throughput |
250 Mbps/500 Mbps/1 Gbps (VMware, KVM), 2 Gbps (VMware) |
| SSL Inspection |
Not available |
1 Gbps (VMware), 900 Mbps (KVM) |
| SSL Connections per Second |
Not available |
1500 (VMware), 900 (KVM) |
| SSL Concurrent Connections |
Not available |
6500 (VMware, KVM) |
| Number of Logical Cores |
2 or 3 |
4 |
| Memory |
8 GB |
16 GB |
| Disk Space |
16 GB |
16 GB |
| IPS Connections per Second |
120,000 (VMware), 60,000 (KVM) |
| IPS Concurrent Connections |
10,000,000 (VMware), 1,000,000 (KVM) |
| Virtual Platform Support |
VMWare ESXi 5.5, 6.0, 6.5, 6.7 (NSX is not required for transparent inspection and enforcement) & KVM – Redhat Enterprise Linux 6, 7 |
| Network Drivers |
VMware- VMNet3
KVM- virtIO |
| Number of Network Segments |
1 |
| Number of Virtual Segments |
No limit |
| Dedicated Management vNIC |
Yes |